TL;DR
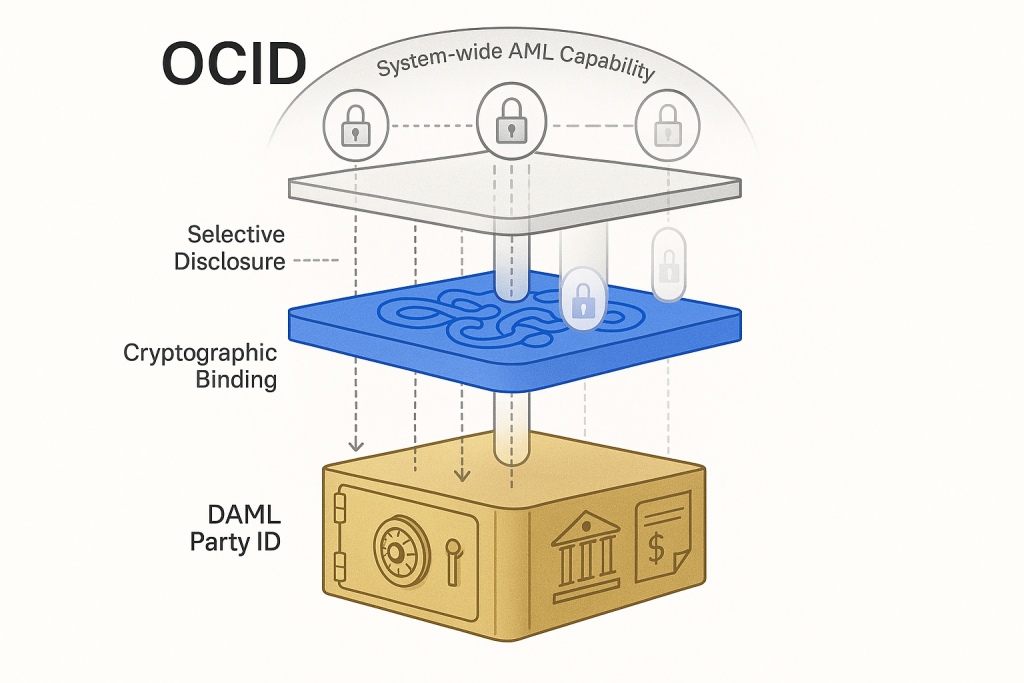
Designing the OCID (Oracle Contract ID) system to connect on-chain and off-chain identities while preserving privacy represented the most complex challenge in our state synchronization implementation. While legacy blockchain identity management focused solely on anonymity within single chains, OCID presents an innovative approach as oracle technology’s first identity management system, enabling system-wide AML (Anti-Money Laundering) while protecting personal information. Through the process of combining DAML Party IDs, zero-knowledge proof-based identities, and cross-chain addresses into a unified identifier, we proved that the technical coexistence of contradictory values—privacy and regulatory compliance—is possible.
The Fundamental Dilemma of Identity Management
The most complex problem we faced while designing oracle state synchronization wasn’t technical implementation. Rather, it was a philosophical question: “For state synchronization to have true meaning, should we be able to know who is who, or should we not be able to know?”
Traditional blockchain philosophy is clear. Anonymity and decentralization are paramount values, and identity is merely a hash of a public key. However, in tokenized capital markets, regulatory compliance is not a choice but a condition for survival. Without KYC/AML, no financial institution can participate, and without participants, state synchronization loses its meaning.
“Interoperability without regulatory compliance has no existential value. But regulatory compliance without privacy is dystopian.”— Early OCID design team meeting notes
The OCID (Oracle Contract ID) concept emerged from this dilemma. Rather than simply solving technical problems, we needed to create a new paradigm that simultaneously realizes the contradictory values of privacy and transparency.

Limitations of Legacy Approaches and New Requirements
Analyzing legacy blockchain identity management solutions, we discovered fundamental limitations. Hyperledger Indy’s Self-Sovereign Identity possessed philosophical elegance in allowing individuals complete control over their identity, but it was incompatible with regulatory oversight requirements. Conversely, legacy centralized identity management contained inherent risks of single points of failure and privacy breaches.
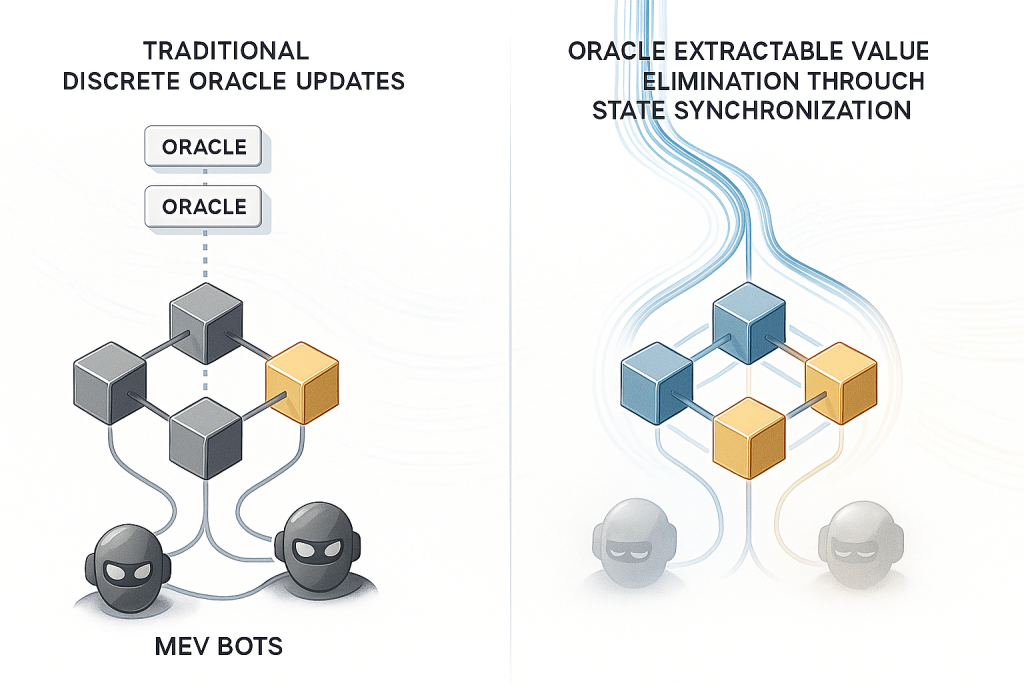
Important Information: Legacy oracle systems never considered identity management at all. Chainlink, for instance, only manages node operator identities while treating data consumer identities as completely anonymous.
Even more complex was the identity consistency problem in cross-chain environments. If the same real person uses 0x123… on Ethereum, 0x456… on Polygon, and alice_bank_001 on CANTON, how could we prove they are the same individual while maintaining anonymity on each chain?
Core requirements OCID needed to address:
- Unified Identity Representation: Consistent identity mapping between on-chain and off-chain systems
- Selective Disclosure: Mechanisms to reveal only necessary identity information
- Regulatory Accessibility: Oversight capability for authorized regulatory authorities
- Cross-chain Consistency: Traceability of the same identity across multiple blockchains
- Privacy Preservation: Protection of personal information from general participants
Birth of the OCID Concept: From Philosophical Approach to Technical Implementation
The core idea of OCID was connecting three different identity systems into a unified identifier. But rather than simple connection, we envisioned a hierarchical identity architecture providing different levels of privacy and transparency at each layer.
{
"ocid": {
"damlPartyId": "alice_institution_001",
"zkId": "0x1a2b3c4d5e6f7a8b9c0d1e2f3a4b5c6d7e8f9a0b1c2d3e4f5a6b7c8d9e0f1a2b",
"chainId": "1"
}
}
The DAML Party ID represents legal identity off-chain, serving as an identifier connected to actual financial institutions or individuals within the CANTON network. The zero-knowledge proof-based zkId represents privacy-preserving identity on-chain, enabling proof of necessary attributes (e.g., adult status, country of residence) without exposing actual identity information. The ChainId follows the EIP-155 standard as a blockchain identifier, providing context in cross-chain environments.
However, the true innovation lay in how these three elements were combined. Rather than simple connection, we designed mechanisms for selectively disclosing different levels of information based on context.
Relationship with RAI: Evolution Toward Standardization
While developing the OCID concept, we realized the need for a more generalized approach. RAI (Regulated Asset Identity) is a concept inspired by OCID but represents a more generalized approach than OCID, conceived during the process of proposing it as an EIP standard.
The core of RAI is providing standardized mechanisms that enable regulatory access while preserving privacy in regulatory compliance token systems. While OCID was a concept specialized for the Oraclizer system, RAI provides a more universal design applicable to all regulatory compliance token implementations.
Tip: The key to RAI implementation is ensuring privacy by storing only cryptographic commitments to identity on-chain, rather than storing personal information directly. Detailed implementation methods can be found in the EIP proposal document.
Realizing System-wide AML: The True Meaning of Technical Innovation
The most innovative aspect of OCID is the possibility of realizing system-wide AML (Anti-Money Laundering). In legacy blockchain systems, AML had to be performed independently on each chain, making it nearly impossible to track cross-chain fund movements.
Through OCID, however, we demonstrated that integrated AML monitoring across the entire system is possible. By connecting and analyzing transactions with the same zkId, we can detect suspicious transaction patterns across multiple chains. Simultaneously, thanks to the zero-knowledge proof characteristics of zkId, actual identities remain unexposed to general participants.
type SystemWideAMLMonitor struct {
zkIdPatterns map[string][]TransactionPattern
riskScoring RiskScoringEngine
alertSystem RegulatoryAlertSystem
}
func (monitor *SystemWideAMLMonitor) AnalyzeCrossChainPattern(
zkId string,
transactions []CrossChainTransaction,
) RiskAssessment {
// Zero-knowledge identity-based pattern analysis
patterns := monitor.zkIdPatterns[zkId]
// Cross-chain transaction correlation analysis
crossChainRisk := monitor.analyzeCrossChainFlow(transactions)
// Integrated risk score calculation
return monitor.riskScoring.CalculateRisk(patterns, crossChainRisk)
}
This is not merely a technical achievement. Simultaneously achieving the contradictory goals of regulatory compliance and privacy protection represents an important milestone in blockchain technology development.
Technical Complexity in the Implementation Process
The most challenging aspect of actually implementing OCID was ensuring the integrity of identity mapping. Malicious actors could attempt to connect another person’s DAML Party ID with their own zkId.
To solve this, we designed a multi-stage verification process:
- Cryptographic Signature Verification: Connections between DAML Party and zkId must be signed with private keys from both identities.
- Time-limited Proof: Connection proofs are only valid within specific timeframes and must be renewed regularly.
- Third-party Attestation: Verification from trusted third parties (e.g., KYC providers) is required.
However, a more fundamental problem was maintaining consistency in cross-chain environments. When addresses with the same zkId exhibit different behaviors on different chains, how do we reconcile them?
Our solution was integrating state synchronization with identity management. The realization that OCID should not simply identify identities but become part of the mechanism ensuring consistency in the state synchronization process.
Philosophical Reflections During Development
While designing OCID, we faced deep philosophical questions beyond technical problems. What is identity? How far should privacy be guaranteed? Where does the legitimacy of regulation come from?
Particularly impressive was implementing the “Need-to-Know” principle. Inspired by DAML’s philosophy, we designed mechanisms ensuring each participant could only access information necessary for their role. This wasn’t simply technical access control but a new approach to the ethical distribution of information.
Reference Information: DAML’s privacy model provides language-level guarantees ensuring each contract participant can only see necessary information. This represents a fundamentally different approach from legacy blockchain’s “everything public or everything private” methodology.
One of our biggest dilemmas was balancing transparency and privacy. We needed to satisfy real-world privacy requirements without compromising blockchain’s fundamental value of transparency. OCID was both a compromise point found in seeking this balance and simultaneously proof of new possibilities.
Future Research Directions and Open Questions
The OCID concept is not complete but a continuously evolving research topic. Challenges to be solved include:
Technical Challenges:
- Securing long-term security through quantum-resistant cryptography integration
- Legal conflict resolution mechanisms in multi-jurisdictional environments
- Supporting large-scale financial networks through scalability optimization
Philosophical Challenges:
- Balance between individual self-sovereign identity and regulatory oversight
- Methodologies for representing collective identity (e.g., corporations, partnerships)
- Temporal modeling of identity evolution
The most important realization from OCID research was that technical innovation alone is insufficient. True innovation occurs at the intersection of technology, regulation, and philosophy. OCID is merely the first result of such convergent thinking.
Moving forward, we plan to further develop OCID into a universal identity management standard. We believe this should not be Oraclizer’s exclusive technology but a common asset that the entire blockchain ecosystem should develop together.
The challenge of identity management is far from over. However, through OCID, we discovered hope that seemingly impossible things might be possible. Isn’t this the true value of research?
References
[1]. Hyperledger Foundation. (2024). Hyperledger Indy: Self-Sovereign Identity Management. https://www.hyperledger.org/projects/indy
[2]. Gupta, S., et al. (2024). Blockchain‐based decentralized oracle network framework for identity management in metaverse environment. Security and Privacy. https://onlinelibrary.wiley.com/doi/10.1002/spy2.414
[3]. ResearchGate. (2023). Privacy-Preserving Identity Management System on Blockchain Using zk-SNARK. https://www.researchgate.net/publication/366842430_Privacy-Preserving_Identity_Management_System_on_Blockchain_Using_zk-SNARK
[4]. Digital Asset. (2025). The tip and the iceberg: Identity and privacy management in Daml and Canton. https://blog.digitalasset.com/blog/daml-smartcontracts-privacy-management-with-canton
[5]. Digital Asset. (2019). Keeping smart contracts private is hard — unless you truly understand them. https://medium.com/daml-driven/keeping-smart-contracts-private-is-hard-unless-you-truly-understand-them-920b31d723e4
[6]. ResearchGate. (2024). Blockchain for Secure Identity Management: A Decentralized and Privacy-Preserving Approach. https://www.researchgate.net/publication/386142804_Blockchain_for_Secure_Identity_Management_A_Decentralized_and_Privacy-_Preserving_Approach